https://linuxconfig.org/how-to-use-arrays-in-bash-script
![bash-logo]() Bash, the
Bash, the
Associative arrays can be created in the same way: the only thing we need to change is the option used: instead of lowercase
Deleting an entire array, it's even simpler: we just pass the array name as an argument to the
Objective
After following this tutorial you should be able to understand how bash arrays work and how to perform the basic operations on them.Requirements
- No special system privileges are required to follow this tutorial
Difficulty
EASYIntroduction
 Bash, the
Bash, the Bourne Again Shell, it's the default shell on practically all major linux distributions: it is really powerful and can be also considered as a programming language, although not as sophisticated or feature-reach as python or other "proper" languages. In this tutorial we will see how to use bash arrays and perform fundamental operations on them. Create an array
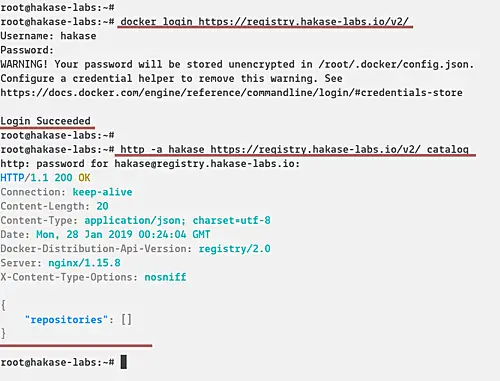
The first thing to do is to distinguish between bashindexed array and bash associative array. The former are arrays in which the keys are ordered integers, while the latter are arrays in which the keys are represented by strings. Although indexed arrays can be initialized in many ways, associative ones can only be created by using the declare command as we will see in a moment. Create indexed or associative arrays by using declare
We can explicitly create an array by using thedeclare command: $ declare -a my_arrayDeclare, in bash, it's used to set variables and attributes. In this case, since we provided the
-a option, an indexed array has been created with the "my_array" name. Associative arrays can be created in the same way: the only thing we need to change is the option used: instead of lowercase
-a we must use the -A option of the declare command: $ declare -A my_arrayThis, as already said, it's the only way to create associative arrays in bash.
Create indexed arrays on the fly
We can create indexed arrays with a more concise syntax, by simply assign them some values:$ my_array=(foo bar)In this case we assigned multiple items at once to the array, but we can also insert one value at a time, specifying its index:
$ my_array[0]=foo
Array operations
Once an array is created, we can perform some useful operations on it, like displaying its keys and values or modifying it by appending or removing elements:Print the values of an array
To display all the values of an array we can use the following shell expansion syntax:${my_array[@]}Or even: ${my_array[*]}Both syntax let us access all the values of the array and produce the same results, unless the expansion it's quoted. In this case a difference arises: in the first case, when using @, the expansion will result in a word for each element of the array. This becomes immediately clear when performing a for loop. As an example, imagine we have an array with two elements, "foo" and "bar": $ my_array=(foo bar)Performing a
for loop on it will produce the following result: $ for i in "${my_array[@]}"; do echo "$i"; done
foo
bar
When using *, and the variable is quoted, instead, a single "result" will be produced, containing all the elements of the array: $ for i in "${my_array[*]}"; do echo "$i"; done
foo bar
Print the keys of an array
It's even possible to retrieve and print the keys used in an indexed or associative array, instead of their respective values. The syntax is almost identical, but relies on the use of the! operator: $ my_array=(foo bar baz)The same is valid for associative arrays:
$ for index in "${!my_array[@]}"; do echo "$index"; done
0
1
2
$ declare -A my_arrayAs you can see, being the latter an associative array, we can't count on the fact that retrieved values are returned in the same order in which they were declared.
$ my_array=([foo]=bar [baz]=foobar)
$ for key in "${!my_array[@]}"; do echo "$key"; done
baz
foo
Getting the size of an array
We can retrieve the size of an array (the number of elements contained in it), by using a specific shell expansion:$ my_array=(foo bar baz)We have created an array which contains three elements, "foo", "bar" and "baz", then by using the syntax above, which differs from the one we saw before to retrieve the array values only for the
$ echo "the array contains ${#my_array[@]} elements"
the array contains 3 elements
# character before the array name, we retrieved the number of the elements in the array instead of its content. Adding elements to an array
As we saw, we can add elements to an indexed or associative array by specifying respectively their index or associative key. In the case of indexed arrays, we can also simply add an element, by appending to the end of the array, using the+= operator: $ my_array=(foo bar)If we now print the content of the array we see that the element has been added successfully:
$ my_array+=(baz)
$ echo "${my_array[@]}"
foo bar baz
Multiple elements can be added at a time: $ my_array=(foo bar)To add elements to an associative array, we are bound to specify also their associated keys:
$ my_array+=(baz foobar)
$ echo "${my_array[@]}"
foo bar baz foobar
$ declare -A my_array
# Add single element
$ my_array[foo]="bar"
# Add multiple elements at a time
$ my_array+=([baz]=foobar [foobarbaz]=baz)
Deleting an element from the array
To delete an element from the array we need to know it's index or its key in the case of an associative array, and use theunset command. Let's see an example: $ my_array=(foo bar baz)We have created a simple array containing three elements, "foo", "bar" and "baz", then we deleted "bar" from it running
$ unset my_array[1]
$ echo ${my_array[@]}
foo baz
unset and referencing the index of "bar" in the array: in this case we know it was 1, since bash arrays start at 0. If we check the indexes of the array, we can now see that 1 is missing: $ echo ${!my_array[@]}
0 2
The same thing it's valid for associative arrays: $ declare -A my_arrayIn the example above, the value referenced by the "foo" key has been deleted, leaving only "foobar" in the array.
$ my_array+=([foo]=bar [baz]=foobar)
$ unset my_array[foo]
$ echo ${my_array[@]}
foobar
Deleting an entire array, it's even simpler: we just pass the array name as an argument to the
unset command without specifying any index or key: $ unset my_arrayAfter executing
$ echo ${!my_array[@]}
unset against the entire array, when trying to print its content an empty result is returned: the array doesn't exist anymore.